The Problem
Communicating over a distance has always presented a challenge to humans. From signal mirrors, semaphore flags, and satellites, people have leveraged technology to overcome communications challenges. In my Army days I had radio relay system in my vehicle that took up half the space, so that I could extend the reach of battlefield commanders to their resources. Today, we take speed, availability, and distance for granted with such innovations as cellular telephony, and Starlink. However, in a mission critical environment such as Command and Control (C2), this presents a unique challenge. The communication must be instant, reliable, and able to reach the responders regardless of where they are and what they may be using for communications. Add to that the need for immediate access to decision makers and experts, and the complications begin to pile up.
How does a dispatcher in an emergency center served via the cloud not only reach their field assets, but the experts and leaders necessary to coordinate a unified response? That dispatcher may be on a console with a Radio over IP (ROIP) interface while the field assets may be on push to talk (PTT) radios, and the experts and leaders who may be travelling and on a cell phone or in conference room located far away in a municipal capital. How does an IT manager securely integrate, provide universal and secure remote access, and archive it for later analysis and compliance? C2 is estimated to be a $45 Billion market with a 6.6 CAGR by 2029. So, solving these problems is not only critical for emergency preparedness, but is a lucrative market for potential vendors.
The Solution
Mass notification services have become standard fare for municipal communications. With one call civic leaders can reach all their residents without sirens or public address systems. These can be further integrated with SMS to send the same message via text messaging, email, or other forms of media. In airports, these systems are used as ‘crash phones’ to bring all the airport emergency services and management together on one system rapidly, securely, and independently of the device they use for communicating. This same concept that has served airport management for years will work in other C2 use cases as well.
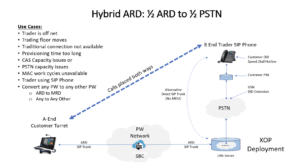
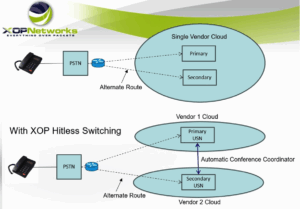
Imagine the first responder on the scene on a handheld radio, their supervisor enroute in a vehicle, the dispatcher at a console in a command bunker, and emergency management resources in a conference room, or in transit. You need one system capable of bringing all of them together. Specifically radio, VOIP telephony, cellular telephony, collaboration and conferencing services, and their underlying infrastructure. To do this you need a common denominator – SIP. XOP Networks provides the pieces required to integrate this secure, reliable, universal service. Their services can be deployed in a highly available manner, using data centers, cloud, premises based, or in a hybrid model.
Starting at the edge, XOP provides a ROIP gateway that can be deployed on a processor in your existing routers, or in a separate dedicated unit or units in a diverse, redundant fashion. They also provide the Universal Service Node (USN) which can convert and bridge any protocol into one conferencing system which supports voice, video, chat, screen sharing, document sharing and does so securely and privately on a platform dedicated to your requirements. XOP also provides device independent access to the USN, so users can dial in from a satellite phone, cell phone, VOIP phone, collaboration system, or use any device with a browser to access the conference. Through its robust API, XOP provides a variety of recording, AI, and other interfaces and integrations to comply with recording regulations and all 3rd party applications and partners with the best of breed MSPs and manufacturers should their customers desire one stop shopping. XOP has even developed custom software and designed CPE telephone stations to meet specific customer requirements. And of course, they provide professional services to manage your project from start to finish and maintain it for the life of the system.
Conclusion
As the technology landscape continues to evolve, ROIP will evolve as well. How will technologies such as AI inference and network slicing provide new features and functionality to this market? Will enhanced mobile broadband/massive machine type communications provide large groups of first responders and their support to areas requiring a temporary or even long-term large emergency services presence? Using the airport crash phone example, how does a regional airport scale to support a massive first responder presence if an incident occurs and lasts for extended periods of time? Access is one portion of the solution, but as the access evolves and presents greater numbers of users, you will require a flexible, scalable, proven collaboration system to integrate and efficiently bridge the audio, video, and sharing for any given situation.
No matter what the future may hold, C2 use cases cannot tolerate service interruption as their constituents face potential life or death situations. XOP networks provides these services in a comprehensive solution that ticks the boxes of technology, compliance, procurement, reliability, and performance. They are acutely aware that the acronym CIA (confidentiality, integrity, and availability) is a critical component of any IT policy. Their solutions have been used by users and vendors to provide over 1 million ports of secure services for over 25 years without a millisecond of downtime. These customers and users include service providers, government, financial institutions, the military, first responders and more.
When you select a vendor partner, you choose one based on experience, reliability, performance, and TCO. XOP excels in these areas as is evidenced by their 25-year history in the very demanding C2 and financial sectors. Is your C2 systems integrator an XOP partner? If not, you may want to have them contact us today for a demonstration and discussion of their solutions. As a former XOP customer, I can assure you that after we did, they were deployed in our cloud environment globally. The value was unparalleled, and the decision was easy to make.
Bill Wagner is a command and control, and financial industry technology consultant with over 30 years’ experience as an industry executive in hardware, software, engineering, operations, R&D, product development and introduction, and strategic development.
Written by:
Bill Wagner, President, Wagner Consulting
 Login
Login